Low-code data governance ensures that policies, roles, and processes are in place to manage how low-code applications are created, deployed, and maintained. This framework helps protect data security, ensures compliance, and maintains data accuracy while empowering non-IT professionals (citizen developers) to build apps under IT oversight. Here’s why it matters and how it works:
- Why it’s important: Only 31% of companies using low-code platforms have governance guidelines, leaving many vulnerable to risks like data breaches and non-compliance.
- Key differences from traditional governance: Unlike rigid IT-centric governance, low-code governance balances centralized security with decentralized ownership. It focuses on challenges like shadow IT and data sprawl.
- Core components: Policies for risk management, role-based access control (RBAC), Data Loss Prevention (DLP) rules, and a Low-Code Center of Excellence (LCCoE) for oversight and training.
- Security essentials: Encryption, multi-factor authentication (MFA), and sandbox environments safeguard sensitive data and prevent misconfigurations.
- Compliance focus: Helps meet standards like SOC 2, GDPR, and HIPAA through audit trails, data classification, and retention policies.
Streamline low code governance in your organization | BRK41
sbb-itb-33eb356
Building a Data Governance Framework for Low-Code
Building a Low-Code Data Governance Framework: 3-Step Implementation Guide
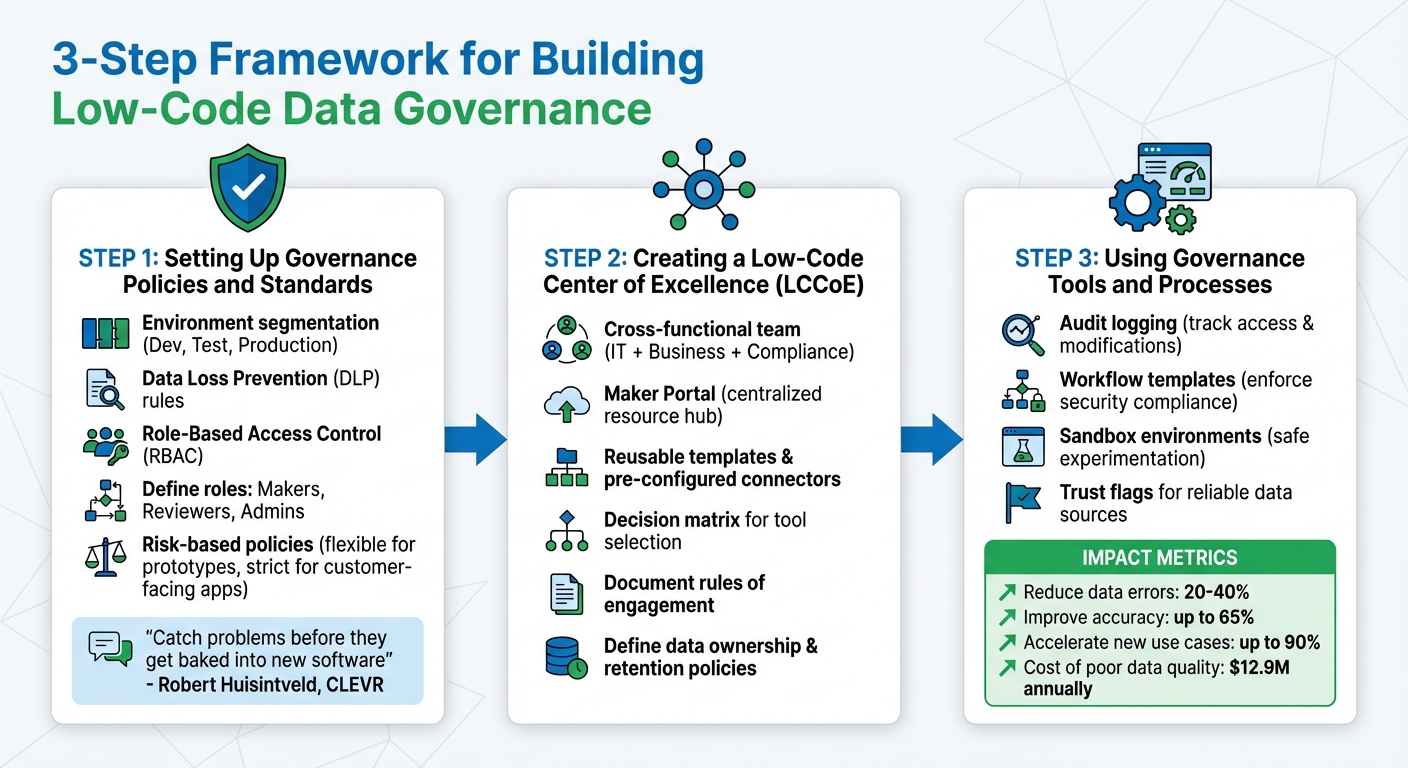
Setting Up Governance Policies and Standards
Establishing clear policies is crucial for managing risk effectively. Begin by defining acceptable practices based on the level of risk involved. For example, use flexible guidelines for prototypes and internal tools, but apply stricter controls for customer-facing applications or those handling sensitive data. This approach safeguards critical systems while avoiding unnecessary slowdowns.
A solid governance framework should include environment segmentation. Separate development, testing, and production environments to prevent untested changes from affecting live systems. Additionally, implement Data Loss Prevention (DLP) rules to control which external connectors or APIs can access sensitive information. As Robert Huisintveld, Team Lead Services NL at CLEVR, explains:
If your governance process includes a design phase, you can catch problems before they get baked into new software.
Addressing potential issues during the design phase saves time and reduces costs.
Another key step is establishing Role-Based Access Control (RBAC). Define roles like "Makers" (citizen developers creating apps), "Reviewers" (responsible for compliance and logic checks), and "Admins" (policy enforcers). This ensures accountability and streamlined operations within your low-code environment.
These foundational policies pave the way for centralized management through a Low-Code Center of Excellence (LCCoE).
Creating a Low-Code Center of Excellence (LCCoE)
A Low-Code Center of Excellence acts as the governance hub, providing oversight, standardization, and training. This cross-functional team brings together IT, business units, and compliance departments to co-manage platform usage. Beyond governance, the LCCoE equips developers with tools like reusable templates, pre-configured connectors, and self-service resources. These resources help citizen developers adhere to best practices without slowing down their workflows.
The LCCoE’s responsibilities include documenting "rules of engagement", defining data ownership and retention policies, and maintaining a Maker Portal. This centralized portal - often hosted on platforms like SharePoint - serves as a one-stop resource for guidelines, templates, and success stories. A practical addition is a decision matrix, a simple guide that helps users choose the right tools and licenses for their needs.
By integrating policies, training, and tools, the LCCoE creates a unified governance framework that supports both compliance and efficiency.
Using Governance Tools and Processes
With policies and centralized oversight in place, automated governance tools ensure that standards are consistently applied. Many modern low-code platforms come with built-in features like audit logging (to track data access and modifications), workflow templates (to enforce security compliance from the outset), and sandbox environments (to allow experimentation without risking production data). These measures are essential, especially when poor data quality costs organizations an average of $12.9 million annually.
Trust flags can also be used to highlight reliable, high-quality data sources. A well-implemented governance framework can significantly reduce data errors - by 20% to 40% - and improve accuracy by up to 65%. Teams adopting a "data-as-a-product" approach can accelerate the launch of new data use cases by as much as 90%. Matt Sullivan, Director of Technical Account Management at Alation, offers this advice:
You start off small with a small set of data and a small set of policies, and then eventually you mature out to more robust processes and tackle additional data domains.
To maintain steady progress, break projects into manageable, time-limited phases. Focus on building smaller, interconnected apps, which simplifies updates and ongoing management.
Security and Access Control in Low-Code Platforms
Setting Up Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) ensures that users only have access to the features and data they need based on their responsibilities. Here's how it works: roles define what a user is responsible for, permissions outline what actions can be performed, and users inherit these roles. As enterprise systems expert Nigel Tape puts it:
Roles map to responsibilities. Permissions map to verbs on specific resources. Users collect roles. That's it.
RBAC should be applied at various levels, from broad areas like workspaces to specific data fields, ensuring precise control. Start with a small set of roles - such as Owner, Admin, Builder, Operator, Approver, Viewer, and External User - and expand only as new responsibilities arise. Assign permissions to groups rather than individuals, as this simplifies both auditing and scaling. If your monthly permission review takes more than one hour, it's a sign your RBAC structure might be overly complicated.
Another helpful feature is security trimming, which hides interface elements users aren't authorized to access. Integration with tools like Single Sign-On (SSO) and SCIM (System for Cross-domain Identity Management) can further streamline user provisioning through identity providers like Okta or Azure AD. For platforms that are self-hosted, a standard 90-day audit log can track changes to permissions. It's also crucial to maintain a strict separation between development and production environments - builders should never have editing rights in live systems.
Beyond access controls, encryption and authentication are key to securing low-code platforms.
Encryption and Authentication Requirements
Data security starts with strong encryption. Use AES-256 for stored data and TLS/SSL to protect data in transit. For particularly sensitive fields, like passwords or payment details, field-level encryption is a smart choice - it encrypts only the critical data without locking down the entire database. When data must be exchanged over less secure channels, asymmetric encryption using RSA keys provides an additional layer of protection.
Adding multi-factor authentication (MFA) strengthens security by requiring a secondary verification step before users can access sensitive information. Support for protocols like SAML 2.0, OpenID Connect (OIDC), and OAuth 2.0 ensures compatibility with enterprise identity systems, while SCIM automates user lifecycle management to immediately revoke access when employees leave. Secrets, tokens, and keys should always be stored in secure vaults - never hardcoded into codebases. UI-level masking can also help by redacting sensitive data, like credit card numbers, so they don't appear in raw interfaces. To avoid issues between environments, keep encryption keys for development, staging, and production separate.
Even with these measures in place, misconfigurations can still pose risks, which we’ll discuss next.
Common Security Challenges and Solutions
Low-code platforms often hide backend complexity, which can lead builders to mistakenly assume that security is automatically handled. In reality, these platforms may use development-friendly defaults, such as open databases or optional authentication, which can leave systems vulnerable. One frequent issue is retrieving entire data tables to the browser and filtering them on the client side - this can expose unauthorized records through browser developer tools.
Another common mistake is hardcoding API keys in frontend code, leaving them visible in the page source. For example, public keys like Supabase's "anon_key" require strict Row-Level Security (RLS) policies to prevent unauthorized access. To address these risks, always enforce server-side validation for API endpoints and database queries. This ensures that role-based restrictions are applied to authenticated sessions. Enable RLS on every database table to limit access to only authorized records. Additionally, sensitive integrations should be handled with server-side proxy functions, such as Supabase Edge Functions or Vercel API routes, to prevent secrets from being exposed in the browser. Always verify webhook signatures from providers like Stripe or GitHub to block unauthorized actions.
Compliance and Risk Management
Compliance and risk management provide the essential framework for handling data responsibly and adhering to regulations, going beyond just security measures.
Meeting Regulatory Standards (SOC 2, GDPR, HIPAA)
Low-code platforms are designed with features that help meet industry regulations. For SOC 2, which emphasizes security, availability, and privacy, these platforms offer tools like audit trails, role-based access controls, and activity logging to track every action taken. With GDPR, the challenge often lies in data residency. Governance frameworks allow organizations to select specific data center locations, ensuring sensitive information stays within required jurisdictions. For HIPAA compliance in healthcare, administrators can label and classify applications containing protected health information (PHI), triggering stricter oversight measures.
Some platforms even provide zero data persistence architectures. This means data is processed in memory and immediately erased without being stored on servers - an essential feature for industries with strict data retention rules. Claire Bunce, Editor at Bizagi, highlights the importance of compliance:
Non-compliance is a costly mistake for businesses. Making sure that applications comply with legal and regulatory requirements reduces the risk of fines and legal issues.
Data Classification and Retention Policies
Good data governance starts with understanding your data's sensitivity. A common approach involves a three-tier classification system:
- Confidential: High sensitivity
- Internal Use: Medium sensitivity
- Public: Low sensitivity
Quickbase underscores the importance of labeling for identifying data sensitivity. While structured data in databases is relatively easy to classify, unstructured data - like emails or shared files - often requires manual labeling. Platforms also enable app-level labeling, where entire low-code apps can be marked as "HIPAA" or "GDPR-sensitive", offering a clear view of which assets require strict governance. Data Loss Prevention (DLP) policies further protect classified data by preventing it from being transferred to unauthorized connectors or external destinations.
These strategies establish a strong foundation for managing risks related to unsanctioned development in low-code environments.
Preventing Shadow IT and Unsanctioned Development
Shadow IT - when employees create apps or automations without IT's approval - poses a significant risk in low-code platforms. The best way to address this is by offering a governed low-code platform that’s fast and efficient, reducing the need for unauthorized workarounds.
Fusion teams, which combine IT, business, and compliance expertise, can co-manage platform usage to ensure applications meet both business and technical standards. This collaborative approach boosts development accuracy by 35.4%. Environment segmentation also plays a key role. By separating development, testing, and production environments, organizations can limit access and prevent unauthorized changes to live applications. Approval workflows ensure all new apps and processes go through internal reviews for design and security compliance before deployment. Centralized audit logs and activity monitoring add another layer of accountability, making it easier to track who’s building what and reducing the risk of rogue development.
Monitoring, Auditing, and Training
Building on a solid governance framework and security measures, continuous monitoring, thorough auditing, and focused training are crucial for maintaining compliance in the ever-changing world of low-code environments. Effective governance thrives on constant oversight and education to ensure compliance stays aligned with the evolving nature of low-code applications.
Tools for Monitoring and Auditing Compliance
Modern low-code platforms integrate automated compliance checks that perform security, operational, and data validations in the background without disrupting development. Real-time monitoring tools quickly identify issues and direct them to the appropriate teams, complete with predefined resolution timelines. Many platforms also incorporate AI-driven automation to flag unused or overly shared components, helping reduce security vulnerabilities.
Centralized auditing tools create detailed activity logs, ensuring traceability across every process. These tools can uncover "orphaned" flows (automations without assigned owners) and track premium license usage to avoid unexpected costs. They also monitor external sharing to prevent data breaches, and advanced document editors provide strict control over file access - an essential feature for industries like government and healthcare.
Data Loss Prevention (DLP) policies further enhance monitoring efforts. Security trimming ensures users only access information relevant to their roles. As Rencore highlights:
A self-service approach, with no clear ownership or oversight, can lead to duplicate reports, inconsistent data, and difficulty maintaining a single source of truth.
This robust monitoring infrastructure lays the groundwork for effective training programs aimed at citizen developers.
Training Citizen Developers on Governance
Training for non-technical developers should emphasize the why behind governance policies to encourage better app-building practices. When citizen developers understand the reasoning behind data handling rules, they’re more likely to create secure and efficient applications. Platforms like Oracle APEX offer starter apps and sample code that align with compliance standards, while enterprise solutions such as Workato and ServiceNow enforce these standards automatically. Additionally, tools like Nintex, which provide process intelligence, can highlight areas where additional training might be necessary.
Using Templates and Sandbox Environments
To complement monitoring and training, secure templates and sandbox environments act as safeguards during development. Pre-built templates include built-in security and compliance requirements, such as data classification, internal-only network restrictions, and secrets management. These templates eliminate the guesswork for citizen developers by embedding governance policies directly into the development process. Features like automated lifecycle constraints - such as default Time-to-Live (TTL) settings (e.g., 14 to 30 days) and cost caps with notification triggers - help maintain control over resources.
Sandbox environments further protect production systems by isolating development and testing. For example, in early 2026, Acme Retail implemented a governance program for marketing micro-apps using pre-filtered CRM views, 14-day TTLs, and $100 monthly cost caps. This approach not only eliminated incidents but also reduced cloud spending by 70% within three months. As Florence.Cloud aptly states:
The goal of governance is to keep speed while reducing risk.
Conclusion
Benefits of Strong Data Governance
Strong data governance turns low-code platforms into valuable business tools while addressing potential security concerns. By implementing solid governance frameworks, organizations can boost security and ensure compliance with regulations like GDPR, HIPAA, and SOC 2. This not only helps avoid costly fines and data breaches but also improves overall data quality - an area where poor practices cost companies an average of $12.9 million annually. Additionally, effective governance minimizes redundant development efforts and lowers long-term maintenance expenses.
Governance also speeds up development by identifying errors early in the process. As Robert Huisintveld, Team Lead Services NL at CLEVR, puts it:
It's cheaper and faster to fix errors before they're written into an application... if your governance process includes a design phase, you can catch problems before they get baked into new software.
Real-world examples back this up. In August 2025, Wesly Van Cleempoel, IT Manager at Duvel Moortgat, shared how the company delivered seven portals and two mobile apps four times faster than traditional methods by adopting a governed low-code approach. Similarly, Andrew Buch Sampaio, Prosegur's Global Director of Systems Engineering, introduced a low-code reskilling program in 2025 that reduced employee turnover and absenteeism by 20%, while seamlessly integrating IT into core business operations.
These examples highlight how governance not only mitigates risks but also provides a competitive edge.
Getting Started with Low-Code Governance
To harness these advantages, start small without disrupting existing workflows. Form a fusion team - a cross-functional group with IT experts, business leaders, and compliance officers - to align technical development with business goals. This collaborative approach has been shown to improve development accuracy by 35.4%.
Introduce tiered guardrails that adapt to the risk level of each application. For prototypes or internal tools, use lighter oversight, while applying stricter controls to mission-critical or customer-facing apps. Developers should work in sandbox environments separate from production systems, and organizations should create libraries of standardized templates that include built-in security and compliance measures. Platforms with automated monitoring and auditing features can save significant time, as data teams often spend 80% of their efforts on discovery, preparation, and protection tasks.
With the low-code market expected to hit $50 billion in revenue by 2028 and only 31% of companies currently having governance guidelines, acting now offers a clear advantage. Mark Tognetti, Global Now Platform Transformation Leader at ServiceNow, emphasizes this point:
A properly deployed low-code platform, with properly enabled and empowered citizen developers and clear governance models, is a whole lot safer than folks building macros in spreadsheets and passing them around via email.
In short, strong governance transforms low-code platforms into secure, agile, and competitive solutions for modern business challenges.
FAQs
How do we decide which low-code apps need strict governance?
To figure out which low-code apps need tighter governance, look at how they affect security, compliance, and data management. Apps dealing with sensitive information or essential processes should be closely monitored to reduce risks and maintain proper control.
What should a Low-Code Center of Excellence actually do day to day?
A Low-Code Center of Excellence (CoE) is like the command center for ensuring low-code platforms are used securely, efficiently, and in line with compliance standards. Its day-to-day responsibilities include establishing clear guidelines, training users, supervising app development, and keeping an eye on how the platform is being utilized.
The CoE plays a critical role in managing access controls, running audits, and enforcing data governance policies. By encouraging best practices and gathering user feedback, it strikes a balance between flexibility and control. This approach supports innovation while ensuring security and compliance remain top priorities.
What are the top low-code security misconfigurations to watch for?
Key security missteps in low-code platforms include weak authentication, poor access controls, exposed secrets, unprotected public endpoints, and insecure default settings. These problems often arise from misconfigured settings, either at the application level or within the tenant setup. Such oversights can leave data exposed and systems vulnerable. Tackling these issues is crucial to keeping low-code environments safe and secure.