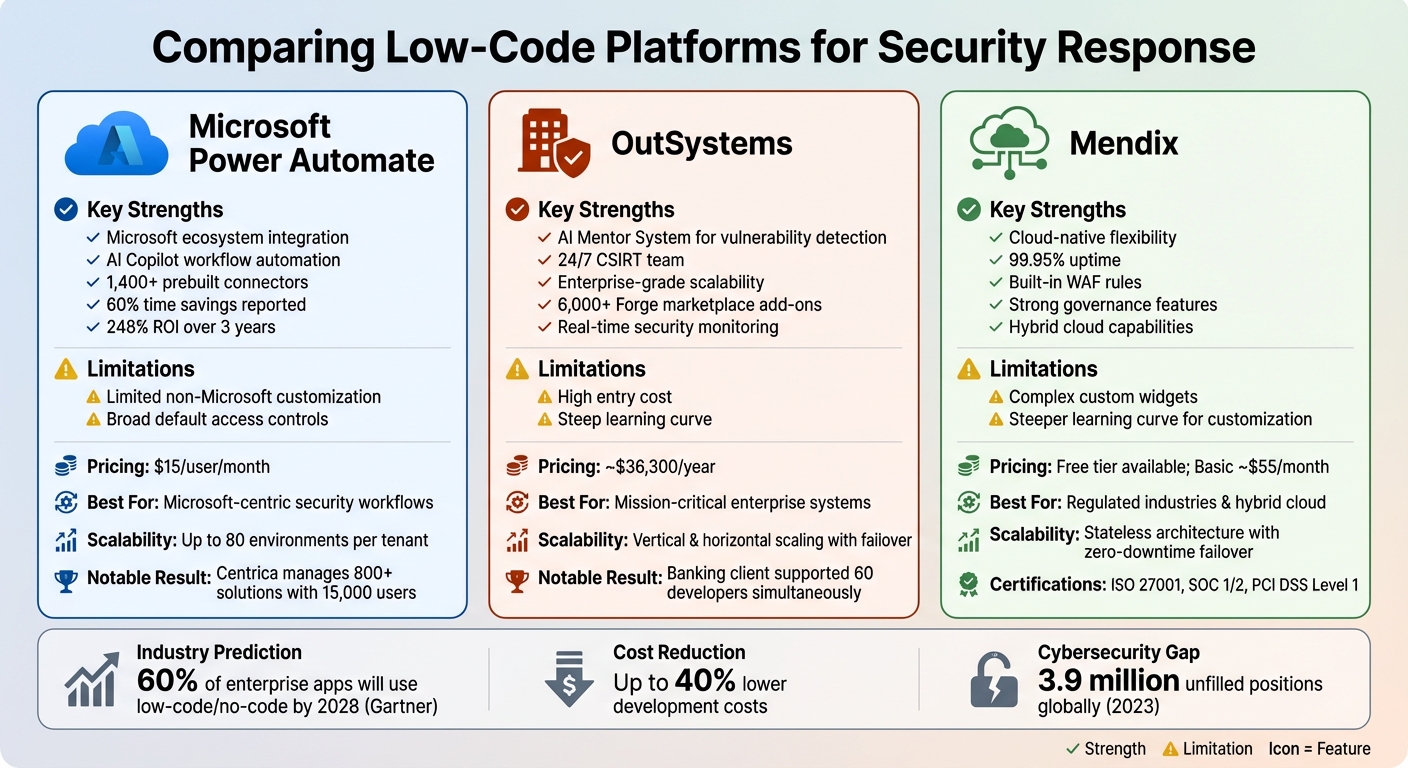
When it comes to responding to security incidents, proprietary low-code platforms are transforming how organizations act quickly and efficiently. By enabling faster deployment of security workflows, these platforms save time, reduce costs, and improve overall security management. This article evaluates Microsoft Power Automate, OutSystems, and Mendix, focusing on their security features, integration capabilities, scalability, and cost-effectiveness.
- Microsoft Power Automate: Best for organizations within the Microsoft ecosystem, offering strong integration with tools like Microsoft Sentinel and Defender. It automates security tasks like account suspension and file access restrictions. Pricing starts at $15/user/month.
- OutSystems: Ideal for enterprises needing advanced security monitoring and AI-driven vulnerability detection. It supports large-scale operations but has a high entry cost (~$36,300/year).
- Mendix: Suited for multi-cloud setups and industries with strict regulations. It provides centralized security management and strong governance features, with a free tier available for small-scale use.
Quick Comparison
| Platform | Key Strengths | Limitations | Starting Price | Best For |
|---|---|---|---|---|
| Microsoft Power Automate | Microsoft ecosystem integration | Limited non-Microsoft customization | $15/user/month | Microsoft-centric workflows |
| OutSystems | Enterprise-grade security tools | High cost, steep learning curve | ~$36,300/year | Large enterprises |
| Mendix | Cloud-native flexibility, governance | Complex custom widgets | Free tier; ~$55/month | Regulated industries, hybrid cloud |
Each platform offers unique advantages depending on your organization's needs. Read on for detailed evaluations of their features, scalability, and pricing to help you choose the right solution for your security workflows.
Low-Code Security Platforms Comparison: Power Automate vs OutSystems vs Mendix
1. Microsoft Power Automate
Security Automation Features
Microsoft Power Automate is designed to tackle security incidents with precision by using custom playbooks triggered by alerts from Microsoft Defender for Cloud Apps. These playbooks can take immediate action, such as suspending compromised accounts, restricting access to sensitive files, or blocking malicious IP addresses. At the same time, they update incident statuses, assign case owners, and apply tags for streamlined tracking and resolution.
Additionally, Microsoft Sentinel keeps an eye on suspicious activities, such as unauthorized app executions, mass deletions, or data destruction. When such incidents arise, Power Automate ensures swift communication by automatically opening tickets in ServiceNow or sending notifications to security teams via Microsoft Teams or Slack.
In July 2024, Jakub Skalbania, acting CTO of Nsure, shared how Copilot in Power Automate drastically reduced the time required to create and configure security workflows - from four hours to just 40 minutes. This efficiency translated into a 60% time savings and a 50% cost reduction.
Integration Capabilities
Power Automate effortlessly connects with a wide array of tools, boasting over 1,400 prebuilt connectors. These include popular security and IT service management platforms like ServiceNow, Jira, SAP, and Salesforce. The platform also integrates seamlessly with Microsoft’s security tools, such as Defender for Cloud Apps, Defender for APIs, and Microsoft Sentinel, creating a unified threat response system. For added protection, Azure Virtual Network (VNet) integration restricts public internet access and ensures traffic is limited to trusted sources.
The platform also supports two-way synchronization with ticketing systems, allowing security teams to manage incidents directly from automated workflows. This level of integration ensures Power Automate is ready to handle the demands of enterprise-level operations.
Scalability and Performance
Thanks to its elastic infrastructure, Power Automate scales automatically to accommodate up to 80 environments per tenant. A great example of its scalability is Centrica, the UK’s largest zero-carbon electricity retailer, which manages over 800 Power Platform solutions and supports 15,000 users while maintaining enterprise-grade governance.
Similarly, CoreLogic has achieved impressive results with Power Automate. Michael O'Brien, Senior Manager for Robotics Automation at CoreLogic, reported saving 50,000 hours annually and achieving a 5x cost reduction using the platform.
"Power Automate has made it really easy to build commonly used functions and piece them together quickly like bricks."
– Michael O'Brien, Senior Manager for Robotics Automation, CoreLogic
Cost Effectiveness
Power Automate offers competitive pricing: $15.00 per user per month for the Premium plan (billed annually) and $150.00 per bot per month for unattended desktop flows. Organizations using the platform have reported a 248% ROI over three years.
For instance, Banco de Crédito del Perú (BCP) saved $80,000 annually and boosted sales by 33%. Employees involved in impactful RPA initiatives also saved an average of 200 hours per year.
With its blend of automation, integration, scalability, and cost efficiency, Power Automate stands out as a powerful solution for rapid and effective security incident response.
sbb-itb-33eb356
2. OutSystems
Security Automation Features
OutSystems, much like Power Automate, prioritizes swift, automated responses to security challenges. What sets it apart is its use of AI-driven monitoring to tackle vulnerabilities proactively. The AI Mentor System scans the low-code model for risks like SQL injection, cross-site scripting (XSS), and unvalidated redirects, alerting developers to potential issues before they deploy their applications. Additionally, the TrueChange engine provides real-time warnings within the IDE during the design phase, helping developers catch problems early on.
When critical vulnerabilities are identified, the OutSystems Development Cloud (ODC) triggers automatic notifications and upgrades at every stage of development. For added protection, OutSystems Sentry offers round-the-clock monitoring, including real-time antivirus scanning for containerized infrastructure and intrusion detection to spot malware or unusual network activity.
The OutSystems Computer Security Incident Response Team (CSIRT) operates 24/7, handling tasks like incident triage, root cause analysis, and mitigation of platform-level threats. Their mission is clear:
"The primary mission of OutSystems CSIRT is to help ensure company, platform, and data preservation by thoroughly investigating computer security incidents and contributing to their prevention."
Integration Capabilities
OutSystems generates standardized JavaScript and .NET code, which makes it easy to integrate with enterprise Static Application Security Testing (SAST) tools. This approach allows businesses to use their existing security scanning tools without needing proprietary solutions, simplifying audits.
The platform also supports seamless integration with enterprise identity systems, including Active Directory, LDAP, OAuth, Single Sign-On (SSO), and Multi-Factor Authentication (MFA). For secure connectivity, the OutSystems Private Gateway creates protected links between cloud apps and on-premises systems. Organizations can also enhance security by layering their own web application firewall (WAF) alongside the platform’s built-in protections.
Moreover, OutSystems is a member of the Forum of Incident Response and Security Teams (FIRST) and participates in the Center for Internet Security (CIS) SecureSuite, ensuring compliance with industry benchmarks.
Scalability and Performance
OutSystems is built to handle enterprise-scale operations, offering both vertical scaling (dynamic CPU and memory adjustments) and horizontal scaling (distributing workloads across multiple servers). The platform ensures high availability through failover mechanisms across multiple zones and load balancing to prevent performance slowdowns during security incidents.
For example, a banking client successfully supported 60 developers working simultaneously in a single development environment without experiencing any performance issues. Features like built-in caching at the page, module, and data levels reduce database strain during high-traffic events. Additionally, Smart Compilation minimizes memory usage, and the platform supports temporary scaling of resources during peak periods.
"The OutSystems architecture allows you to set up an environment that scales to accommodate large numbers of developers so they can work simultaneously without being hindered by performance issues."
– OutSystems Evaluation Guide
Cost Effectiveness
OutSystems' flexible scaling options help organizations manage costs by temporarily increasing resources during security incidents and scaling back during normal operations. Automated security patching also reduces the need for manual intervention in addressing vulnerabilities.
For mobile apps, the AppShield add-on strengthens native Android and iOS applications against tampering and reverse engineering. This is particularly crucial given the global cybersecurity workforce shortage, with 3.9 million unfilled positions reported in 2023.
Product Marketing Manager Anya Syulina highlighted an industry-wide trend across low code platforms, citing Gartner’s recommendation:
"use GenAI 'to help solve a number of perennial issues plaguing cyber security, particularly the skills shortage and unsecure human behavior'"
By automating repetitive tasks like log reviews and vulnerability scans, OutSystems helps bridge the cybersecurity talent gap, freeing up resources for more strategic work.
Next, we’ll explore how Mendix approaches secure and scalable incident response workflows.
3. Mendix
Security Automation Features
Mendix employs a model-driven approach that simplifies managing access rights by centralizing them within a single domain model. It also incorporates built-in Web Application Firewall (WAF) rules to guard against OWASP Top 10 vulnerabilities, cutting down on the need for manual code reviews and reducing the likelihood of errors.
The Mendix AI Assistance (Maia) includes a Best Practice Recommender, which identifies and resolves security issues in real time as developers work on applications. To ensure uninterrupted operations, Mendix Cloud features automated failover and auto-recovery mechanisms that maintain business continuity during outages. Additionally, when critical vulnerabilities like Log4j arise, the platform's Software Composition visibility tool helps teams quickly gauge the impact across their entire application portfolio.
For ongoing threat management, Mendix employs CrowdStrike for round-the-clock endpoint security and runs a bug bounty program via HackerOne to uncover potential vulnerabilities. Frank Baalbergen from Mendix highlights the platform's advantages:
"Low-code development platforms, specifically Mendix, are a good solution to these challenges because you are able to standardize at a platform level where a lot of the security features are provided out of the box."
These built-in security tools work seamlessly with external systems, enhancing overall breach response capabilities.
Integration Capabilities
Mendix integrates with third-party Static Application Security Testing (SAST) tools like Snyk, VeraCode, and SonarCube to strengthen application security and speed up incident response workflows. It uses Micrometer, a neutral instrumentation facade, to connect with centralized monitoring systems, improving intrusion detection efforts. For identity management, Mendix supports SAML 2.0, OpenID, and Azure AD, ensuring compatibility with corporate single sign-on policies.
API access is secured using Personal Access Tokens (PATs), which limit delegated access and are automatically revoked when a user is deactivated, helping to contain security breaches quickly. Mendix also supports a range of industry-standard data integration protocols, including REST, SOAP, JDBC, OData, and MQTT. For organizations requiring higher security, Mendix Cloud Dedicated offers a private AWS-hosted environment that can be connected via VPN, completely isolating applications from public internet access.
This extensive integration capability ensures Mendix remains scalable and secure, even during security incidents.
Scalability and Performance
The stateless architecture of Mendix applications enables smooth failover between runtime containers without disrupting users. The platform includes Application Performance Monitoring (APM) to keep track of CPU and memory usage during security events. For enterprise users, it offers zero-downtime failover by distributing user loads across multiple runtime containers within the same availability zone, ensuring continuous operation during incidents.
As a cloud-native, containerized platform, Mendix supports auto-provisioning and auto-healing, allowing it to scale effortlessly as needed without requiring major architectural changes. Its certifications, such as ISO/IEC 27001:2022, SOC 1 Type II, SOC 2 Type II, and PCI DSS V4 Level 1 Service Provider Attestation of Compliance, further underline its reliability and security standards.
Cost Effectiveness
Mendix allows users to start developing and testing for free, with enterprise licenses unlocking advanced features like zero-downtime failover. Its model-driven design and centralized Control Center not only simplify security management but also lower ongoing maintenance costs.
The platform's Control Center lets organizations assign a centralized Security Contact email, ensuring that critical alerts reach the appropriate personnel. Additionally, its Quality and Security Management (QSM) feature automates ISO 25010 static analysis, reducing the reliance on manual code reviews.
Is Low-Code Secure? OutSystems Security Explained for CISOs with Fred Gruhn
Strengths and Weaknesses
Let’s break down the key strengths and challenges of the platforms discussed earlier. Each brings its own set of advantages and trade-offs when it comes to managing security incident response.
Microsoft Power Automate stands out for its seamless integration within the Microsoft ecosystem and its AI Copilot feature, which simplifies workflow creation. However, it struggles with integrating older or non-Microsoft systems, and its default access controls may be overly broad unless carefully configured.
OutSystems is a top choice for enterprise-grade incident response systems. Its AI Mentor system promotes proactive security and performance improvements, while the Forge marketplace offers access to over 6,000 pre-built add-ons and connectors. Additionally, its "Sentry" tier provides advanced security monitoring. On the downside, the platform has a steep learning curve for beginners and comes with high entry costs, with Developer Cloud plans starting at about $36,300 annually.
Mendix offers cloud-native flexibility and strong governance features, boasting 99.95% uptime and excellent audit trails for industries like finance and healthcare. Its hybrid cloud capabilities and microservices architecture make it ideal for complex data integration. As Raymond Reyes explains:
"Mendix excels in scenarios involving Business Process Automation, making it a strong choice for applications requiring workflow automation, including processes like request approvals, document management, and other business workflows".
That said, Mendix has a steeper learning curve for creating custom widgets and can experience occasional glitches in advanced custom coding.
Here’s a quick comparison of each platform’s strengths, weaknesses, pricing, and ideal use cases:
| Platform | Primary Strength | Key Weakness | Starting Price | Best For |
|---|---|---|---|---|
| Microsoft Power Automate | Ecosystem integration & AI Copilot | Limited non-Microsoft customization | $15/user/month | Microsoft-centric security stacks |
| OutSystems | Enterprise scalability & AI Mentor | High entry cost & complexity | ~$36,300/year | Mission-critical enterprise systems |
| Mendix | Cloud-native agility & governance | Steeper curve for custom widgets | Free tier; Basic ~$55/month | Hybrid cloud & regulated industries |
Across all platforms, common challenges include the risk of "Shadow IT" caused by unsupervised tool development and poorly configured access controls by citizen developers. Despite these risks, organizations using tools like the Power Platform can lower development costs by up to 40%. Furthermore, Gartner predicts that by 2028, 60% of enterprise applications will be created using low-code or no-code platforms.
These insights, combined with the technical evaluations shared earlier, can help you identify the platform that aligns best with your incident response requirements.
Conclusion
Choosing the right low-code platform for security response boils down to your organization's size, infrastructure, and automation goals. If your business already relies on the Microsoft ecosystem, Microsoft Power Automate is a cost-effective option at just $15 per user per month. Its seamless integration with Office 365 and Azure makes it ideal for streamlining internal security workflows.
For larger enterprises handling mission-critical security systems, OutSystems stands out. With a starting price of $36,300 annually, it offers the scalability and performance needed for large-scale operations. To maintain protection as you grow, follow best practices for scaling low-code applications securely. Its AI Mentor System provides security analysis every 12 hours, though it comes with a steeper learning curve.
On the other hand, Mendix shines in multi-cloud setups and complex, distributed architectures. It's particularly suited for fostering collaboration between technical and non-technical teams.
As Katie Bykowski from Swimlane aptly puts it:
"Low-code security automation makes it possible to respond quickly and effectively to today's complex challenges... without the need to hire more people".
FAQs
Which platform is best if we already use Microsoft Sentinel and Defender?
For organizations already using Microsoft Sentinel and Microsoft Defender, Sentinel stands out as the top choice for managing security incidents and streamlining incident response. Its seamless integration with Microsoft Defender XDR allows for a centralized approach to handling security threats, significantly improving detection and response times.
What sets Microsoft Sentinel apart are its advanced tools. With built-in AI, machine learning, and automation, it simplifies complex workflows and enhances efficiency. If your organization is already invested in Microsoft security solutions, Sentinel is designed to complement and maximize their capabilities.
How do these platforms prevent Shadow IT and over-permissioned workflows?
Low-code platforms tackle issues like shadow IT and over-permissioned workflows by incorporating features such as role-based access control (RBAC) and advanced permission management. With tools like detailed user roles, Single Sign-On (SSO), and compliance controls, these platforms ensure that only authorized users have the ability to create or modify workflows. By enforcing strict access policies, they help prevent unauthorized app development while maintaining secure and well-regulated workflows throughout an organization.
What should we budget for licensing and scaling incident-response automations?
When planning a budget for incident-response automations in low-code platforms, several factors come into play - pricing models, integration requirements, and extra features all influence costs.
Licensing costs typically fall between $10,000 and $25,000+ per year, with per-user fees ranging from $15 to $60 monthly. If you're looking to scale, expect additional charges for things like AI modules, API usage, or extra storage.
To stay prepared, aim for a flexible annual budget of $10,000 to $50,000, keeping in mind that costs may increase as your automation needs expand.