Low-code development platforms are growing rapidly, but only 21% of organizations have formal governance policies in place, leaving many exposed to risks like security breaches, compliance failures, and technical debt. To address these challenges, here are five practical governance frameworks:
- Risk-Tiered Governance: Categorizes apps into tiers (low, moderate, high risk) based on their impact and data sensitivity, applying oversight proportionate to each tier.
- Low-Code Center of Excellence (LCCoE): Establishes a dedicated team to standardize practices, enforce policies, and monitor low-code projects across the organization.
- Policy and Standards Framework: Sets clear rules for data handling, access control, and development processes to ensure consistency and safety.
- Continuous Monitoring and Audit: Provides real-time tracking of changes, user actions, and potential vulnerabilities to prevent risks before they escalate.
- Security Governance: Focuses on proactive safeguards like encryption, multi-factor authentication (MFA), and automated compliance checks to protect sensitive data.
These frameworks help organizations balance speed and control, ensuring low-code tools drive results without compromising security or compliance. Combining these approaches can create a robust governance strategy tailored to your needs.
Creating a Power Platform governance framework by Antti Pajunen
sbb-itb-33eb356
1. Risk-Tiered Governance Framework
A Risk-Tiered Governance Framework organizes low-code applications into different levels based on their potential impact, data sensitivity, and user reach. This method ensures that not all apps are treated equally. Instead, it applies oversight that matches the app's complexity - lighter controls for simpler tools and stricter reviews for critical systems.
Risk Categorization
The framework typically consists of three tiers:
- Tier 1 (Low Risk): Covers tools like expense trackers or team calendars. These apps handle non-sensitive data, have small user bases, and require minimal review. Platform guardrails manage their oversight.
- Tier 2 (Moderate Risk): Includes apps with broader user bases, internal system integrations, or access to business-critical (but non-personal) data. These require targeted security and integration approvals.
- Tier 3 (High Risk): Encompasses customer-facing apps, those processing personal or financial data (e.g., GDPR/HIPAA compliance), or apps integrating with regulated systems. These undergo detailed architectural and compliance reviews similar to traditional software.
Interestingly, only 21% of organizations have formal policies for low-code development, yet 75% of IT leaders express concerns about security and governance. Automated tools on low-code platforms can help by assigning risk tiers based on data connectors or APIs used. With this clear categorization, centralized oversight ensures each tier gets the appropriate level of control.
Centralized Oversight
Centralized oversight is key to managing this framework effectively. IT teams or a Center of Excellence set global standards and define "safe build zones", intervening only for high-risk applications. As We LowCode explains:
"The goal is not to control every application - but to control the system that produces applications".
This approach shifts the focus from manually reviewing every app to managing the platform itself. High-risk apps, such as those accessing customer databases, are automatically flagged for closer review, making the framework scalable.
Security and Compliance
Baseline security measures, like encryption and multi-factor authentication (MFA), are built into the platform, ensuring all tiers maintain a standard level of protection. Automated audit logs also track who modifies an application and what data is accessed, promoting accountability without slowing down low-risk development. Kissflow summarizes this approach well:
"Governance becomes a guardrail rather than a gate".
2. Low-Code Center of Excellence (LCCoE) Framework
To manage the risks of low-code development effectively, organizations are increasingly turning to a structured approach: establishing a dedicated Center of Excellence. This setup helps balance the need for speed with the necessity of maintaining control.
A Low-Code Center of Excellence (LCCoE) is a specialized team responsible for guiding, standardizing, and scaling low-code projects across an organization. Acting as a link between IT and business units, it ensures that projects align with broader enterprise goals. With projections indicating that 75% of new applications will rely on low-code or no-code technologies by 2026, having a structured oversight mechanism has never been more important.
Centralized Oversight
The LCCoE takes a comprehensive approach to managing low-code platforms, creating a framework of standards that includes approved UI templates, integration patterns, and data models. This structured approach not only streamlines the development process but also reduces the need for manual reviews. For instance, organizations with mature Centers of Excellence report 67% faster solution delivery, while those without proper governance face security violations at rates 3 to 4 times higher. As Quickbase aptly puts it:
"A CoE provides the framework to scale low-code safely, reduce shadow IT, and eliminate... manual, repetitive, and inefficient tasks that hold organizations back".
Policy Enforcement
Beyond oversight, the LCCoE plays a crucial role in enforcing policies that ensure consistency across all projects. This includes implementing Data Loss Prevention (DLP) policies, separating development, testing (UAT), and production environments, and employing role-based access control (RBAC). Many organizations are now adopting federated models, where IT defines the standards, but business units are empowered to innovate within those boundaries. Additionally, structured training programs provided by the LCCoE can lower security risks by 40% to 50%, equipping citizen developers with the knowledge they need for proper data management before they gain access to production systems.
Monitoring and Auditing
To maintain accountability, the LCCoE ensures continuous monitoring of application performance, user activities, and change histories through automated audit trails. Organizations with a CoE report a 72% improvement in security posture and compliance outcomes compared to those without formal governance. This approach shifts the focus from periodic audits to real-time compliance monitoring, allowing teams to address potential issues before they escalate into significant problems.
3. Policy and Standards Framework
A Policy and Standards Framework is the backbone of secure low-code development, complementing the structure offered by a Center of Excellence. It establishes clear rules and guidelines to ensure safe and efficient practices. However, despite the rapid adoption of proprietary low-code platforms, only 21% of organizations have formal policies for no-code development. This gap leaves many businesses exposed to avoidable risks.
Risk Categorization
A key feature of this framework is its use of risk-based tiering to categorize applications. These tiers include:
- Tier 1: Low-risk tools, such as departmental prototypes.
- Tier 2: Moderate-risk applications that handle internal business data.
- Tier 3: High-risk systems, such as customer-facing apps or those subject to regulatory requirements.
This categorization allows organizations to match the intensity of controls to the level of risk. For instance, lightweight oversight might suffice for internal prototypes, while high-stakes applications demand stricter reviews.
Policy Enforcement
Once risk tiers are defined, specific controls can be implemented. These include:
- Role-Based Access Control (RBAC) and Multi-Factor Authentication (MFA) to manage access.
- Data classification systems that organize information into public, internal, and restricted categories.
- Integration policies requiring the use of approved connectors for ERP and CRM systems, with IT review mandated for custom API integrations to prevent data breaches.
To streamline compliance, many organizations now automate these controls directly within the low-code platform.
Security and Compliance
The framework also emphasizes both preventive and detective security measures. For example:
- Approved UI templates and security modules are mandatory.
- Development, testing, and production environments are segregated to isolate experimental apps from live systems.
- Citizen developers are often required to complete certification programs before deploying their applications.
Concerns about security and governance are widespread - 75% of IT leaders highlight these as key issues with no-code platforms. However, structured training programs can help mitigate these risks significantly. As stated in the Low-Code Manifesto:
"Governance & Control: Robust governance and control processes and protocols are essential".
Additionally, lifecycle management policies, including app retirement procedures, are vital to avoid orphaned applications and reduce technical debt.
4. Continuous Monitoring and Audit Framework
Building on structured control frameworks, continuous monitoring takes risk management to a new level by providing real-time insights. A Continuous Monitoring and Audit Framework transforms governance from occasional reviews to ongoing oversight. Instead of relying on quarterly assessments, this framework tracks every application change, user action, and data access event in real time. This constant vigilance enables automated detection of vulnerabilities as they arise.
Monitoring and Auditing
At the heart of this framework lies audit logging, which creates an unchangeable record of every action within the low-code environment. These logs capture critical details, such as who made changes, what was altered, and when it occurred. For instance, if a citizen developer adds a new API connector or modifies data access permissions, the system automatically logs the event. Many organizations integrate these logs into their SIEM (Security Information and Event Management) tools, ensuring seamless visibility across their IT infrastructure.
Automated scanning works continuously in the background, identifying vulnerabilities before they reach production. This includes detecting exposed secrets like hardcoded API keys, insecure API calls, or attempts at unauthorized data exfiltration. Deployment gates then block applications with unresolved security issues from going live. As Superblocks explains:
"Low‑code governance is the set of policies, controls, and processes that keep low‑code applications secure and compliant at scale".
Centralized Oversight
Beyond logging and scanning, centralized oversight brings all monitoring data together in one place. Governance platforms offer centralized dashboards, giving IT teams a comprehensive view of the entire low-code ecosystem. For example, tools like the Mendix Control Center allow administrators to track developer activities, monitor operational health, and detect unauthorized "shadow IT" applications. This centralized approach is essential, as Johan den Haan from Mendix emphasizes:
"If you can't see what people are doing, you can't make sure they're doing the right thing".
Security and Compliance
Ongoing risk assessments play a vital role in identifying issues such as identity impersonation or excessive data sharing. Software composition analysis provides an inventory of third-party dependencies and libraries, helping organizations uncover supply-chain risks from outdated components. Given that low-code applications often depend on external APIs, continuous monitoring becomes indispensable. Third-party API providers can make unexpected updates, potentially disrupting integrations or exposing sensitive data. For this reason, API testing and security analysis must be a continuous process rather than a one-time effort.
5. Security Governance Framework
A Security Governance Framework is all about staying ahead of potential threats, rather than just reacting to them. While continuous monitoring keeps an eye on activity within your low-code environment, this framework sets up proactive safeguards. These guardrails help protect against data breaches, unauthorized access, and compliance issues, creating a secure foundation for development.
Risk Categorization
Not all low-code applications come with the same level of risk. Risk classification focuses on protecting sensitive data and avoiding security breaches. Applications should be categorized based on factors like the size of the user base, the type of data they handle (such as GDPR or HIPAA-regulated information), and whether they’re internal or customer-facing. For example, a mission-critical system managing customer payment data will require thorough validation, while a basic departmental workflow might only need minimal oversight. This tiered approach ensures that IT resources are used efficiently, avoiding unnecessary bottlenecks.
Policy Enforcement
Strong security governance depends on automated policy enforcement rather than manual checks. Organizations can establish a library of pre-approved connectors for commonly used systems like ERP and CRM platforms, embedding security controls such as rate limiting. Automated tools can block unauthorized API use and prevent non-technical users from creating databases without IT approval.
Key measures include:
- Role-Based Access Control (RBAC): Restricts access so users only see what’s necessary for their role.
- Multi-Factor Authentication (MFA): Reduces the risk of identity theft.
- Data Protection Guardrails: Enforce encryption both at rest and in transit.
- Data Loss Prevention (DLP): Safeguards sensitive information with strict policies.
Automating these policies ensures security and compliance without creating extra work for teams.
Security and Compliance
Real-world incidents highlight why security governance is so critical. For instance, in July 2022, Carousell, a marketplace app in Singapore, exposed the private data of 3.4 million users because a public-facing API lacked proper filtering during a chat feature update. Similarly, in August 2024, U.S.-based telehealth provider Confidant Health left a database unprotected, exposing 1.7 million activity logs and 120,000 files, including therapy notes and ID scans, due to a misconfiguration.
As Infosprint Technologies aptly puts it:
"If IT doesn't know it exists, it cannot secure it".
Automated tools can help by scanning for vulnerabilities like exposed APIs, unencrypted data, or overly permissive access settings. Yet, only about 12% of code commits currently include automated security scans - a figure that underscores the need for more robust adoption of these tools.
Centralized Oversight
Automated controls are just one piece of the puzzle. Centralized oversight ensures that security management is consistent across the low-code environment. A Center of Excellence (CoE) can serve as the central authority for setting security standards, reviewing critical applications, and monitoring platform usage across the organization. This team should include both IT security experts and business stakeholders to ensure that policies are practical and enforceable.
Platform-specific tools, like the Mendix Control Center or Microsoft Managed Environments, offer a single dashboard for tracking low-code activity. Maintaining a cross-platform inventory of apps, connectors, and data objects is crucial for eliminating "shadow IT" blind spots. Additionally, development sandboxes can limit access to production resources during the building phase, keeping IT in the loop about what’s being created.
Framework Comparison Table
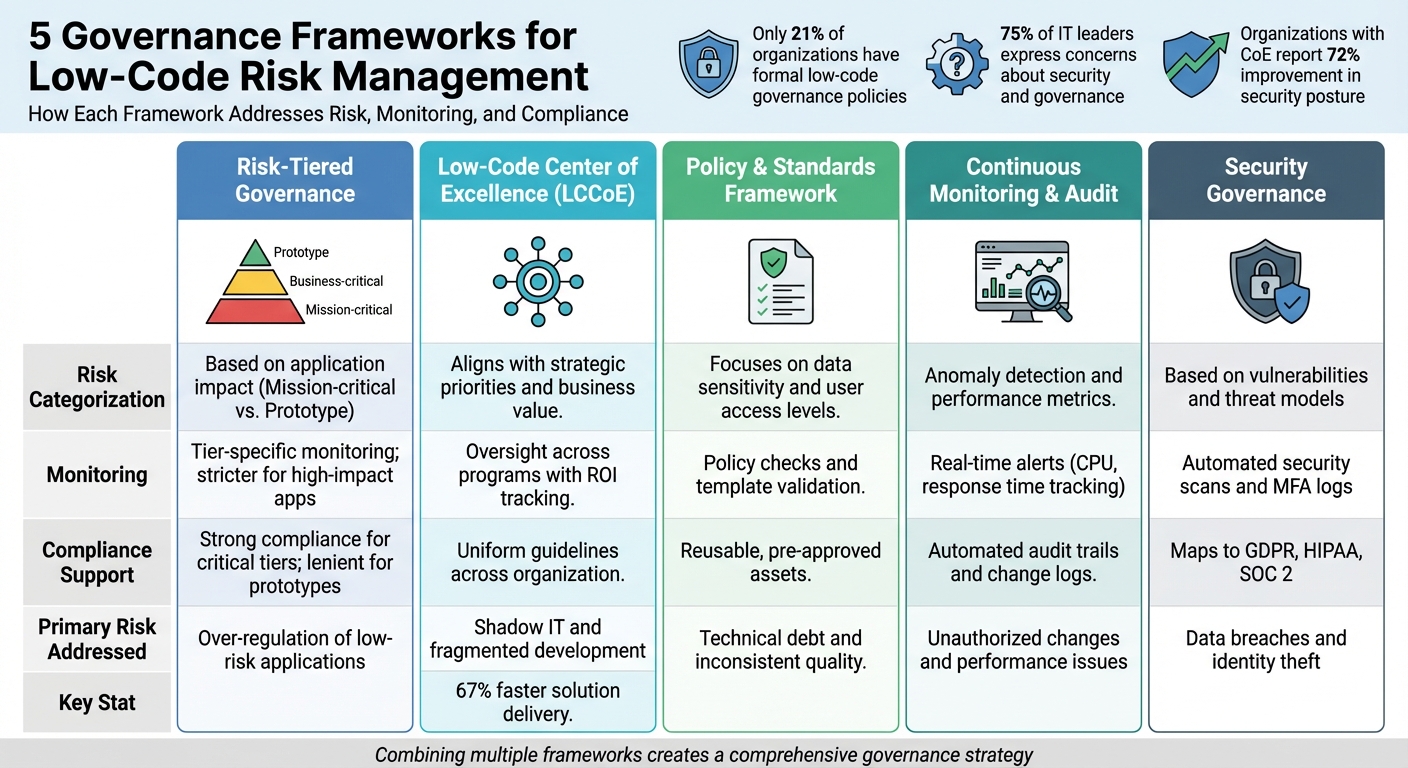
Comparison of 5 Low-Code Governance Frameworks for Risk Management
This table outlines how different frameworks handle risk categorization, change monitoring, and compliance support, along with the primary risks they aim to address.
| Governance Framework | Risk Categorization Method | Monitoring Capabilities | Compliance Support | Primary Risk Addressed |
|---|---|---|---|---|
| Risk-Tiered | Classifies based on application impact (e.g., Mission-critical vs. Prototype) | Tier-specific monitoring; stricter for high-impact applications | Strong compliance for critical tiers; more lenient for prototypes | Over-regulation of low-risk applications |
| LCCoE | Aligns with strategic priorities and business value | Oversight across programs with ROI tracking | Provides uniform guidelines across the organization | Shadow IT and fragmented development efforts |
| Policy & Standards | Focuses on data sensitivity and user access levels | Ensures adherence through policy checks and template validation | Leverages reusable, pre-approved assets for compliance | Technical debt and inconsistent quality standards |
| Continuous Monitoring | Uses anomaly detection and performance metrics | Offers real-time alerts, including CPU or response time tracking | Automated audit trails and detailed change logs | Unauthorized changes and performance issues |
| Security Governance | Evaluates based on vulnerabilities and threat models | Employs automated security scans and tracks MFA logs | Maps to regulatory standards like GDPR, HIPAA, and SOC 2 | Data breaches and identity theft risks |
The table highlights how each framework tackles specific risk management challenges. For instance, Continuous Monitoring provides robust compliance support through automated audit trails and real-time SIEM integrations, while Security Governance shines in areas like RBAC, encryption, and MFA to meet regulations such as GDPR, HIPAA, and SOC 2.
A combined approach that integrates these frameworks can enhance risk management by blending strategic oversight with advanced technical safeguards.
Conclusion
Low-code platforms are growing rapidly, yet only 21% of organizations have formal no-code policies in place. This leaves many businesses vulnerable to security breaches, compliance issues, and inefficiencies.
Strong governance provides the guardrails teams need to innovate quickly while staying secure. Whether it's stopping shadow IT through a Center of Excellence, safeguarding data with security protocols, or using tiered oversight based on application risk, these frameworks help ensure low-code tools deliver results without creating unnecessary risks. As Mendix aptly states:
"Governance is the difference between a portfolio that sings and just having a bunch of apps".
The five governance frameworks discussed address unique challenges, but combining them creates a more robust safety net. By implementing tiered guardrails, automating compliance processes, and building reusable asset libraries, organizations can scale low-code development while maintaining enterprise-level standards. Together, these strategies form a comprehensive governance plan.
Equally important is choosing the right platform to support governance efforts. Platforms with features like RBAC (Role-Based Access Control), automated audit trails, and sandbox environments make it easier to put governance into action. The Low Code Platforms Directory is a helpful resource for finding platforms tailored to specific needs, whether that's GDPR compliance, HIPAA readiness, or real-time monitoring.
To get started, take stock of your current low-code applications, assess their risk levels, and align the appropriate governance frameworks with your compliance and development goals. With the right structure in place, low-code can shift from being a potential risk to becoming a strategic advantage.
FAQs
How do I decide an app’s low-, moderate-, or high-risk tier?
To determine an app’s risk tier, consider several key factors: the sensitivity of the data it handles, compliance requirements, access controls, and its potential impact on operations.
- Low-risk apps: These typically deal with non-sensitive data, have limited access permissions, and pose minimal risk to business operations.
- Moderate-risk apps: These apps handle sensitive information, require stricter access controls, and could disrupt some processes if compromised.
- High-risk apps: These are responsible for managing regulated or highly confidential data, involve broad access permissions, and are critical to security or compliance efforts.
Using governance frameworks can provide clear guidance for assessing these risks and ensuring effective management strategies.
What should a Low-Code Center of Excellence (LCCoE) actually own?
A Low-Code Center of Excellence (LCCoE) plays a critical role in managing and guiding low-code development within an organization. Its key responsibilities include establishing governance policies, implementing security controls, maintaining compliance standards, overseeing application lifecycle management, and monitoring all low-code development activities. By focusing on these areas, the LCCoE ensures that low-code platforms are used safely, efficiently, and in compliance with organizational and regulatory requirements.
Which governance controls should be automated in the platform first?
Automating governance controls in key areas like deployment environments, data access, and change tracking is a smart first step. These areas play a huge role in maintaining security, compliance, and auditability, which are essential for managing low-code platforms effectively. By addressing these aspects early, you can build a strong foundation for a secure and well-regulated development process.